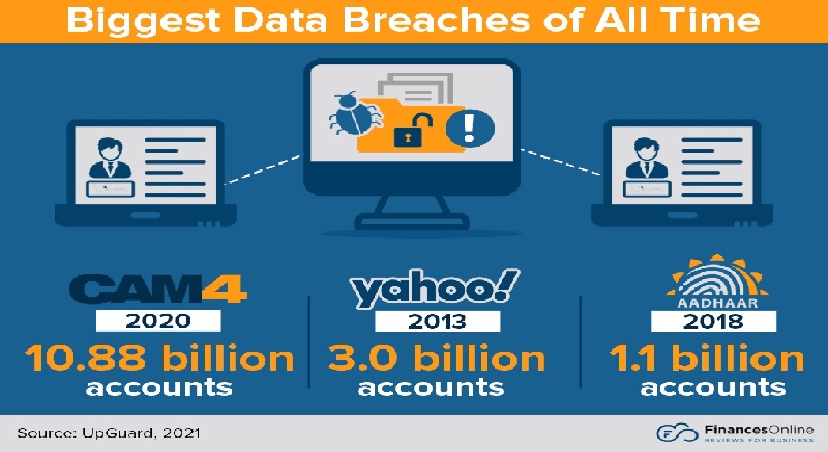
No one wants to deal with data breaches but during COVID, it seems like malware and hackers are sitting at ambush to hit vulnerable businesses. I was watching a crime show on Spectrum Specials which inspired me to do some research on the current cybersecurity statistics. Turns out, the year 2020 didn’t just bring the Coronavirus pandemic, but the Cyber pandemic as well!
Just in the first 3 quarters of 2020, 2953 breaches were reported publicly. A lot more happened, which is why everyone from businesses to individuals was requested to stay vigilant. If you have become a victim of a breach, and looking for some advice on how to handle it, you need to look at this:
Table of Contents
Toggle1: Look Into Your Incident Response Plan
In case you don’t have one, work on it right away. But if you do have it, open that document. It outlines what your firm, workers, and third parties should do if a data breach occurs.
Ensure that your employees are aware of the plan and are properly trained to handle it. Employees who panicked and made mistakes are frequently the ones who cause the most damage in a data leak. During a data breach, having an incident response strategy can prevent confusion and fear.
2: Identify the Source of the Breach
Determine the source and scope of the breach so that you can respond quickly. Intrusion detection and or prevention systems (IDS & IPS) should ideally be in place to automatically log such security incidents.
You can use these logs to find out where the breach originated, which files were accessed, and what actions the intruder took. This will make everything quick and easy. Plus, the next steps will require this information.
3: Alert Your Task Force
Alert your teams right away. It’s normally the task force that handles everything related to IT. In case you don’t have one, assemble this breach task team as soon as possible to deal with the breach.
If you have an IPS solution in place, it may be able to assist you in proactively responding to the breach by taking measures to prevent intruders. Even if you have an IPS solution, you should have a team ready to deal with a breach just in case.
The course of action you will need to take will depend on the severity of the breach, but experts recommend storing a disc image or copy of the affected servers for legal reasons when the breach happens. Also, if an employee account was used in the attack, immediately revoke that account’s access and order all other employees to reset their passwords.
4: Contain the Data Breach
The most important thing to do while handling the breach is to contain it. You mustn’t delete everything that’s infected. In fact, you must contain the breach and prevent it from spreading. Command your IT professionals to isolate the areas that have been affected from the rest of the business.
Other than this, disconnect from the internet and disable all remote access. During this time, restrict the internet traffic as well and change all access control credentials.
5: Keep the Communication Open
NEVER hide the breach from your employees or stakeholders.
Not sure how to break the news? Seek legal guidance for determining the right course of action when it comes to telling the public, the customers as well as your employees. You wouldn’t want to end up with a penalty because you failed to notify your stakeholders in time.
It’s best if the public learns about the data leak from you, the company. If you wait too long to tell them, it will appear as if you are trying to hide something. Decide when you want to inform your consumers and keep in mind that the sooner the better. Include as much information as possible regarding the type and scope of the breach. If a customer’s information has been compromised, make them aware of the information that was taken.
If necessary, provide your customers with a course of action or next steps to take after the breach.
6: Contact a Law Firm
Legal complications can arise. Therefore, it’s in your best interest to find a law firm within your legal region and discuss your matter.
You would have to notify the data breach to your local authorities such as Homeland Security if you are USA-based and Interpol Cybercrime Division if you are Europe-based. It depends on the laws governing your country and the type of data your firm owns. These organizations may be able to provide additional details about the assault and assist you in recovering your data. A positive relationship with your local law enforcement department could be beneficial.
In the end, learn from your mistakes, improve your security and prepare an incident response plan that’s better than the previous one.